L’articolo è stato aggiunto alla lista dei desideri
IBS.it, l'altro eCommerce
eBook in lingua straniera
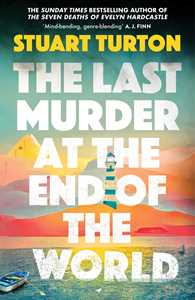
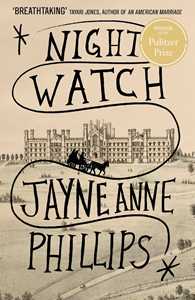
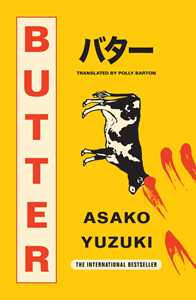
In evidenza
Scopri i nostri consigli di lettura: classici o novità da leggere in lingua inglese
Classici da riscoprire
Una selezione di classici da leggere in lingua originale
Top Reparti Fiction
eBook a piccoli prezzi
Una selezione di eBook in inglese per tutte le tasche!
Saggistica
Saggi indispensabili per comprendere l'attualità, riscoprire la Storia, stimolare la curiosità
Top Reparti Saggistica
Su IBS trovi migliaia di eBook in italiano e oltre 1 milione di eBook in inglese in formato ePub subito scaricabili. Tantissime novità da leggere, eBook di prossima uscita che puoi prenotare e ricevere sul tuo eReader. Un intero catalogo di eBook a tua disposizione che puoi navigare per reparto: puoi scegliere per esempio tra Fiction, History, Science, Computer & Technology, Children & Teens, Business, Economics & Law e molto altro. Nell'area dedicata alle promozioni eBook sono raccolte tutte le offerte in corso, migliaia di eBook sempre scontati che si rinnovano continuamente. Non perderti gli eBook Solo per oggi, dove ogni giorno puoi scegliere un eBook tra una selezione di titoli a prezzo fortemente scontato fino alla mezzanotte. Naviga nelle nostre pagine: tantissimi eBook da leggere sugli eReader Kobo. Grazie alla nostra app di lettura gratuita leggi anche su pc, tablet e smartphone. Scopri qui come regalare un eBook.
Nella pagina degli eBook universitari e professionali puoi navigare facilmente tra i titoli dedicati alla formazione e al lavoro, manuali e test: migliaia di titoli subito disponibili e pratici da consultare.
IBS è partner ufficiale dell'iniziativa Carta del Docente e Carta della Cultura Giovani e del Merito. È possibile acquistare, utilizzando le Carte Cultura, solo prodotti venduti e spediti da IBS.